Your OEM customer asks about your security process. Do you have one?
Even sensors, chips, and simple parts need vulnerability handling — at the latest when the customer demands it. Complioty makes getting started as easy as possible.
OEMs are professionalizing their requirements. Suppliers without a security process are dropped.
Expectation gap
OEMs demand security evidence — you have no process, no policy, no contact person. Not out of negligence, but because it was never an issue before.
No team
You have 80 employees and no security specialist. Building a PSIRT sounds enterprise — but without a process you're unprepared for inquiries.
Getting started is the problem
You know you need to act. But the tools on the market are built for large organizations. You need an entry point that fits your size.
What happens if you wait?
Your OEM customer switches to a competitor who has a documented security process. Not because your part is bad — but because you can't prove it.
Finally make yourself visible.
Integrators expect structured advisories — you have no process
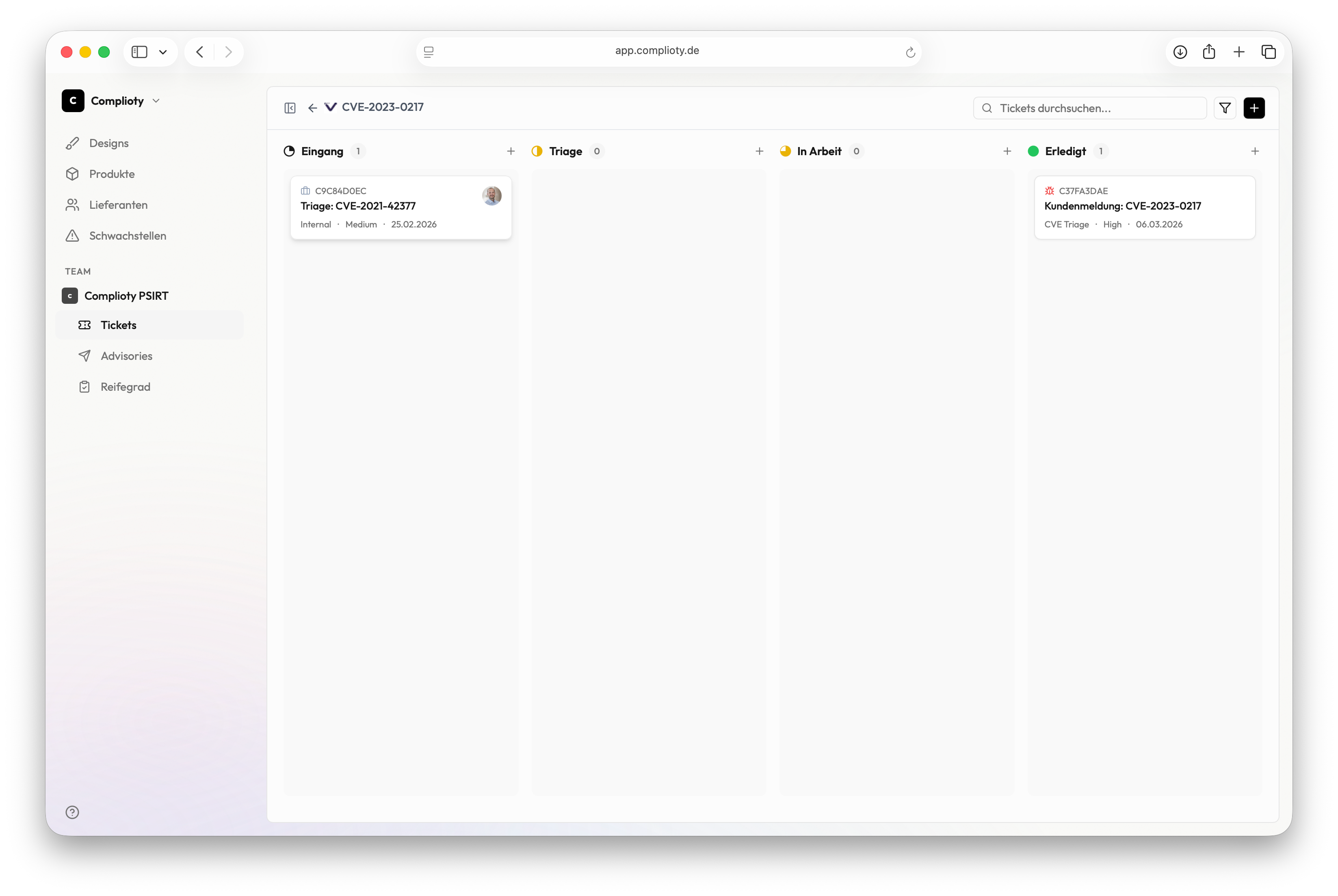
Case management with CSAF advisories, security.txt and CVD policy
Your first month with Complioty
Create account, set up product
You create your first product and configure the basic data. Complioty guides you step by step.
security.txt & CVD policy live
Within minutes you have a security.txt and a CVD policy — the two things OEMs look for first.
Public disclosure page is up
Your professional disclosure page is live. Security researchers and customers see: there is a process here.
First case completed
You've created a test case, assessed it, and generated a CSAF advisory. You know the workflow and you're prepared.
Ready for OEM inquiries
When the next supplier questionnaire comes, you have answers: process, policy, contact path, advisory format.
In two weeks you have a professional security process — without building a team first.