Full control over the security of your products.
You're responsible for product security — but you lack the tools to truly stay on top of it. Complioty gives you the overview you need.






The Problem
The attack surface grows. Your tooling doesn't.
You can't see what's inside your products.
Connected products, dozens of components, supplier software — and your overview consists of Excel spreadsheets, scattered PDFs, and the memory of individual developers. If a CVE appears tomorrow, you don't know if your products are affected.
Vulnerabilities appear daily. You find out by chance.
Every new CVE could affect your products. Without a system, you manually search the NVD and hope you don't miss anything.
You can't prove security — only claim it.
The auditor comes. The buyer asks. Your boss wants a status. You have gut feeling, but no evidence.
The Risk
What happens when product security remains a matter of chance?
The Incident
A critical vulnerability is discovered in a supplier component. You don't know which of your products are affected. It takes you days to find out. Your customers know before you do.
The Blind Spot
Your product has been in the field for months. A known CVE affects an embedded library. Nobody on the team noticed. The buyer of your biggest customer asks about your security status. You have no answer.
The Regulatory Hammer
From September 11, 2026, vulnerability reporting is mandatory. From December 11, 2027, the Cyber Resilience Act applies in full. Manufacturers who cannot demonstrate security lose market access.
No process. No evidence. No market access. And the trust of your customers? Gone.
The Challenge
Stop manually solving what can't be solved manually.
Product security doesn't fail due to lack of knowledge. It fails because you spend 80% of your time searching, mapping, and documenting — instead of doing security.
80%
of your time goes to administration
14 days
for audit preparation — per audit
48h
until you know who's affected by a CVE
We know your reality
Built by experts who know the problem.
Small teams, too many tasks, wrong tools. Complioty is built for exactly this reality.
BMBF Funding
0k €
PhD Theses
0
Made in Munich
DE
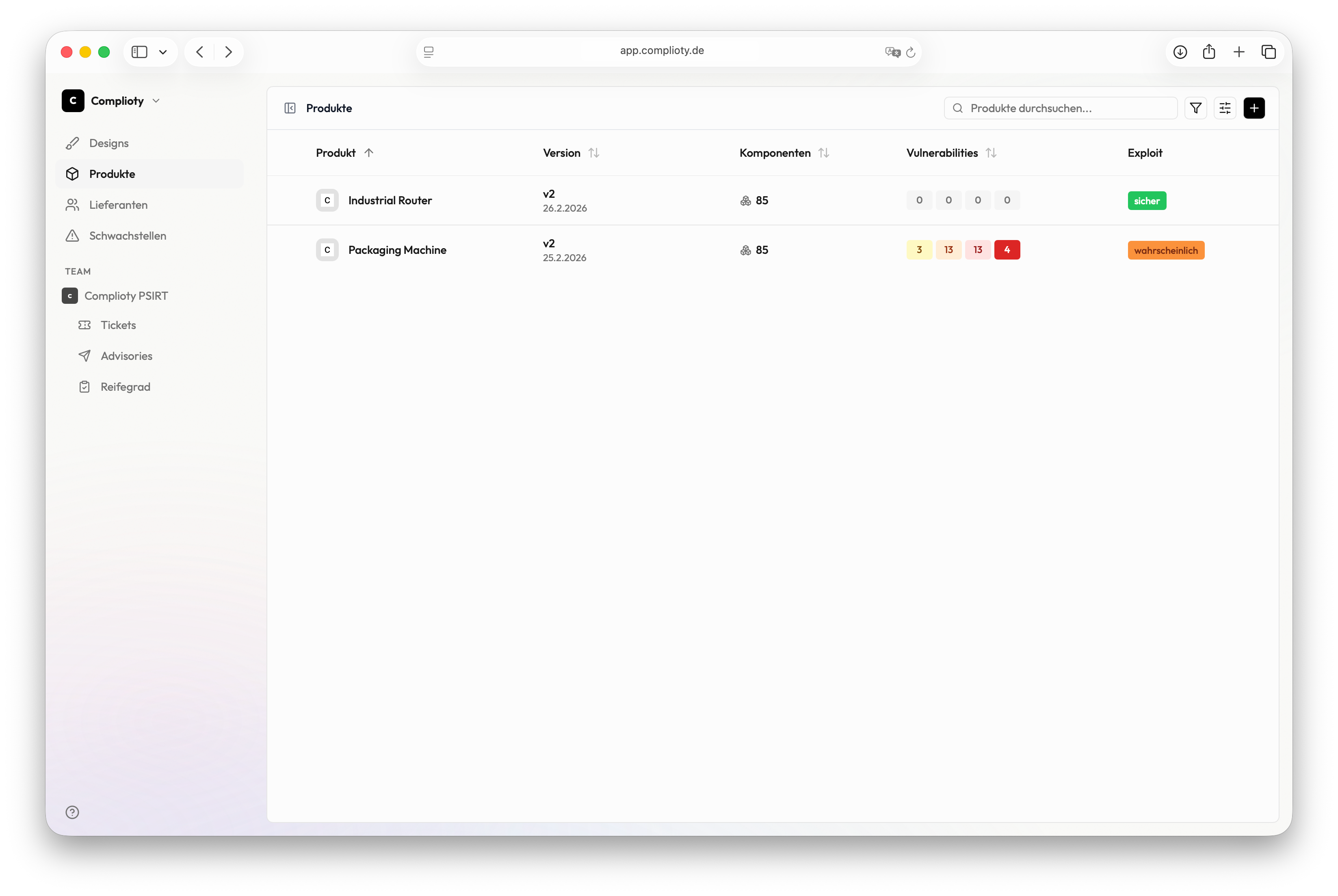
How it works
Product security in three steps.
01
Start with what you have.
Import products — done.
02
See what's going on.
Vulnerabilities, risks, priorities — automatically.
03
Stay in control.
Fix, document, prove — continuously.
No SBOM to import yet?
Solutions
For your industry.
Complioty adapts to the requirements of your industry.
Machinery & Plant Manufacturers
Complex machines, connected controls, long lifecycles — Complioty makes product security manageable for mechanical engineering.
Component Manufacturers
Suppliers are under pressure to provide security evidence. Complioty helps make compliance visible along the supply chain.
Parts Manufacturers
From sensor to actuator — Complioty helps parts manufacturers systematically detect and fix vulnerabilities.