Your component is in hundreds of products. Every vulnerability is multiplied.
As a component manufacturer, you are the origin of the supply chain. When a CVE surfaces with you, all downstream OEMs are affected. Complioty gives you the tools to respond quickly and professionally.
One vulnerability at your end affects hundreds of products at your customers.
Multiplier effect
Your component is in hundreds of end products. A single vulnerability multiplies across all OEMs — and you are the source.
PSIRT pressure
OEMs expect fast, structured responses. Without a PSIRT process you're unprepared for inquiries and lose trust with every incident.
Product family explosion
Dozens of firmware variants, different hardware revisions, various customer configurations. Every CVE must be assessed against all variants.
What happens if you wait?
A CVE in your firmware goes public. 200 OEM customers ask about the status at the same time. You have no answer.
The right app for every challenge.
New CVEs in your firmware libraries are discovered too late
Automatic monitoring across all product families and firmware versions
OEMs expect structured advisories — you have no process
Case management with CSAF advisories, security.txt and CVD policy
No transparency about third-party components in your firmware
SBOM tracking and supplier risk assessment for your own supply chain
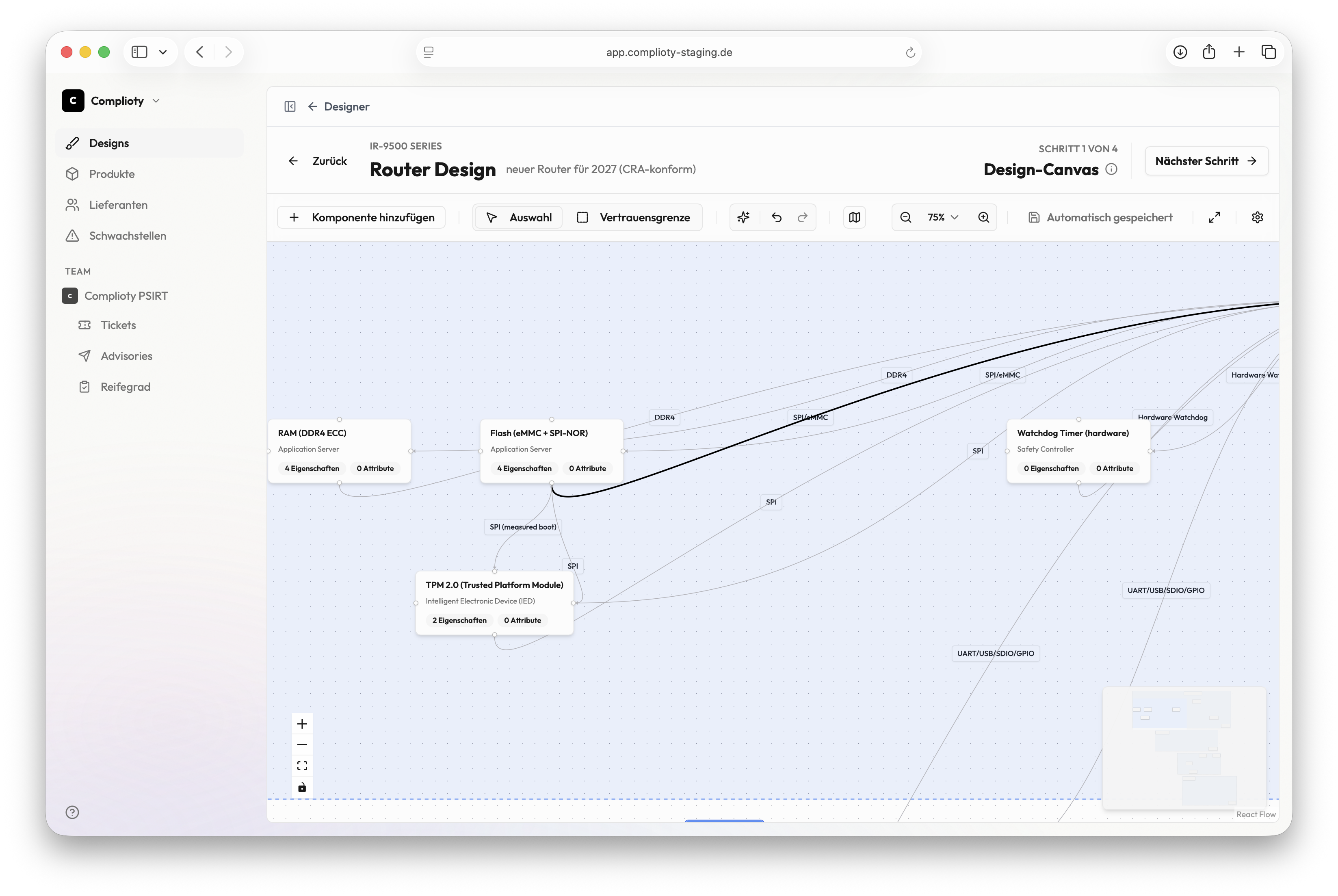
No systematic threat analysis for component architectures
Threat modeling with STRIDE and MITRE ATT&CK — at component level
Scenario: Critical CVE in your firmware library
Critical CVE in your firmware library
Observer raises the alarm: A critical CVE affects a library used in your central firmware platform.
Affected product families identified
Tracer immediately shows which product families and firmware versions are affected — including the OEMs using those variants.
Case opened and assessment started
A case is created in Notifier. The team assesses the impact per product family and prioritizes communication.
CSAF advisory generated
A machine-readable advisory is created — with all affected products, CVSSv3 score and recommended actions.
OEMs notified, disclosure page updated
Affected OEMs are notified. The public disclosure page shows the current status. Documentation is complete.
From discovery to OEM notification — in under two hours instead of two weeks.