Detect vulnerabilities before they become a problem.
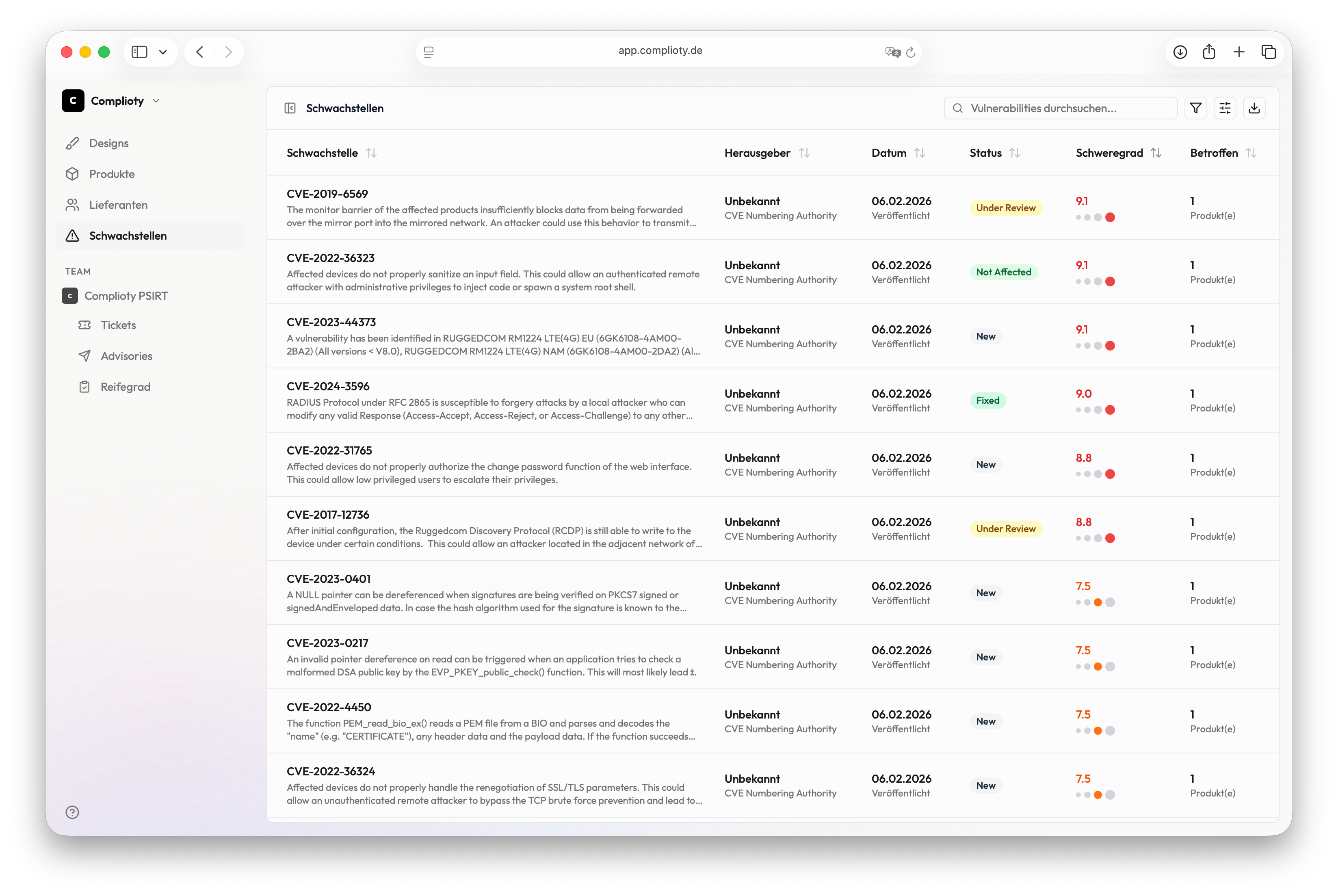
Automatic CVE detection, EPSS-based prioritization and triage management — for all products at a glance.
The Moment
Monday, 8:14 AM. Your colleague sends a link: "Have you seen this? Critical CVE in OpenSSL." You know: At least three of your products use OpenSSL. But which version? In which component?
Two days later you have the answer. Two days during which the vulnerability was public while you searched through Excel spreadsheets and asked colleagues who installed which version.
With Observer you open the dashboard. The CVE is already detected, assigned to the affected products and prioritized in the matrix. EPSS says: 87% exploit probability in 30 days. You escalate directly to Notifier — before the coffee gets cold.
Features
Comprehensive vulnerability overview — automatic, prioritized and connected.
Automatic CVE Detection
Observer automatically detects new vulnerabilities for all components of your products — around the clock, without manual searching.
NVD Enrichment
Each CVE is enriched with complete data from the National Vulnerability Database: CVSS score, description, references.
EPSS Integration
The Exploit Prediction Scoring System shows you how likely a vulnerability will be exploited in the next 30 days.
Triage Management
Evaluate, prioritize and document each vulnerability. Status tracking from "New" to "Closed" — everything traceable.
Cross-Product Overview
One dashboard for all products. See at a glance which product has how many open vulnerabilities.
Case Escalation to Notifier
Escalate critical CVEs to Notifier with one click — for structured handling and disclosure.
How Observer works
Register products
Enter your products with their components and software versions. Observer then knows what to look for.
CVEs automatically detected
Observer continuously scans the NVD and other sources. New vulnerabilities are automatically assigned to your products.
Prioritize matrix
The Vulnerability Matrix shows you at a glance: high CVSS + high EPSS = act immediately.
Perform triage
Evaluate each vulnerability: Does it affect your product? Is there a workaround? Document your decision.
Escalation & treatment
Critical cases are escalated as cases to Notifier. The rest is documented and closed.