Supplier security based on real data.
Automatic analysis of your suppliers' security maturity — based on publicly available signals, not questionnaires.
The Moment
You get the questionnaire back. 47 questions, all answered. "Yes, we have a security process." "Yes, we respond to vulnerabilities." "Yes, we have a PSIRT." Sounds good. Check.
Then the CVE comes. Critical, in a component from this supplier. You look for a security.txt — doesn't exist. CVD policy? None. CSAF advisory? Nothing. The score: 25 out of 100.
With Tracer you would have known beforehand. Not because someone checked "Yes", but because Tracer checks what's really there: security.txt, CVD policy, CSAF feed, PSIRT. Real signals instead of self-assessment.
Features
Supply chain security based on facts — not on trust.
Automatic Supplier Detection
Tracer automatically detects suppliers from your product data and component lists — no manual table maintenance.
security.txt Detection
Tracer automatically checks whether your suppliers have published a security.txt according to RFC 9116 — the first indicator of security maturity.
CVD Policy Detection
Does the supplier have a Coordinated Vulnerability Disclosure Policy? Tracer finds out and evaluates the quality.
CSAF Feed Detection
Tracer detects whether suppliers publish CSAF advisories — machine-readable security notices according to international standards.
PSIRT Analysis
Does the supplier have a Product Security Incident Response Team? Tracer analyzes the publicly available information.
Maturity Level (0-5)
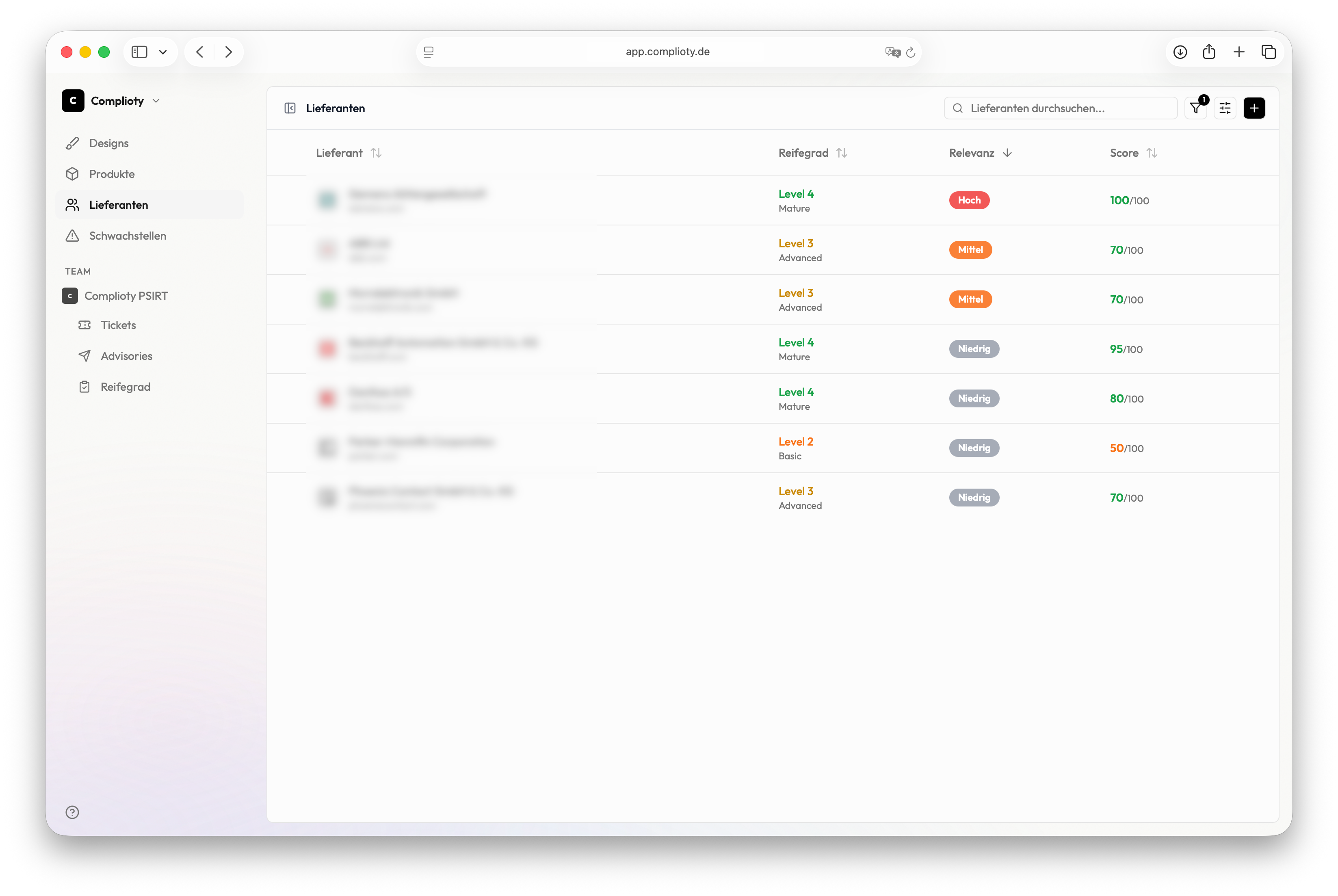
The maturity level shows at a glance how far a supplier is in their security maturity — from "no signals" to "best practice".
How Tracer works
Suppliers detected
Tracer automatically detects suppliers from your product data — or you add them manually.
Security presence analyzed
Tracer scans the public security presence of each supplier: security.txt, CVD policy, CSAF feed, PSIRT.
Scores calculated
From the detected signals, Tracer calculates a security score (0-100) and a maturity level (0-5).
Risks identified
The risk matrix shows you immediately which suppliers are critical — and why.
Continuous monitoring
Tracer continuously monitors changes. If a supplier removes their security.txt, you see it immediately.