Threat Modeling with AI — in hours, not weeks.
Upload product data, the AI creates the architecture model. Identify threats with STRIDE and MITRE ATT&CK, assess risks, assign mitigations.
The Moment
Your team is developing a new edge controller with an OPC-UA interface. The project manager asks: "Do we have a risk analysis?" The answer: A Word document from 2019 that nobody touches anymore.
So someone sits down. Three weeks later: 40 pages that will be outdated again at the next audit. No link to real threats. No connection to the CVEs that Observer is currently reporting.
You upload the product specification — a PDF, a draw.io, a DOCX. Designer recognizes components, interfaces and data flows automatically. The AI creates an initial architecture model and suggests damage scenarios. You refine instead of starting from scratch. And when something changes, you version — instead of rewriting.
Features
Everything you need for professional threat modeling — in one tool.
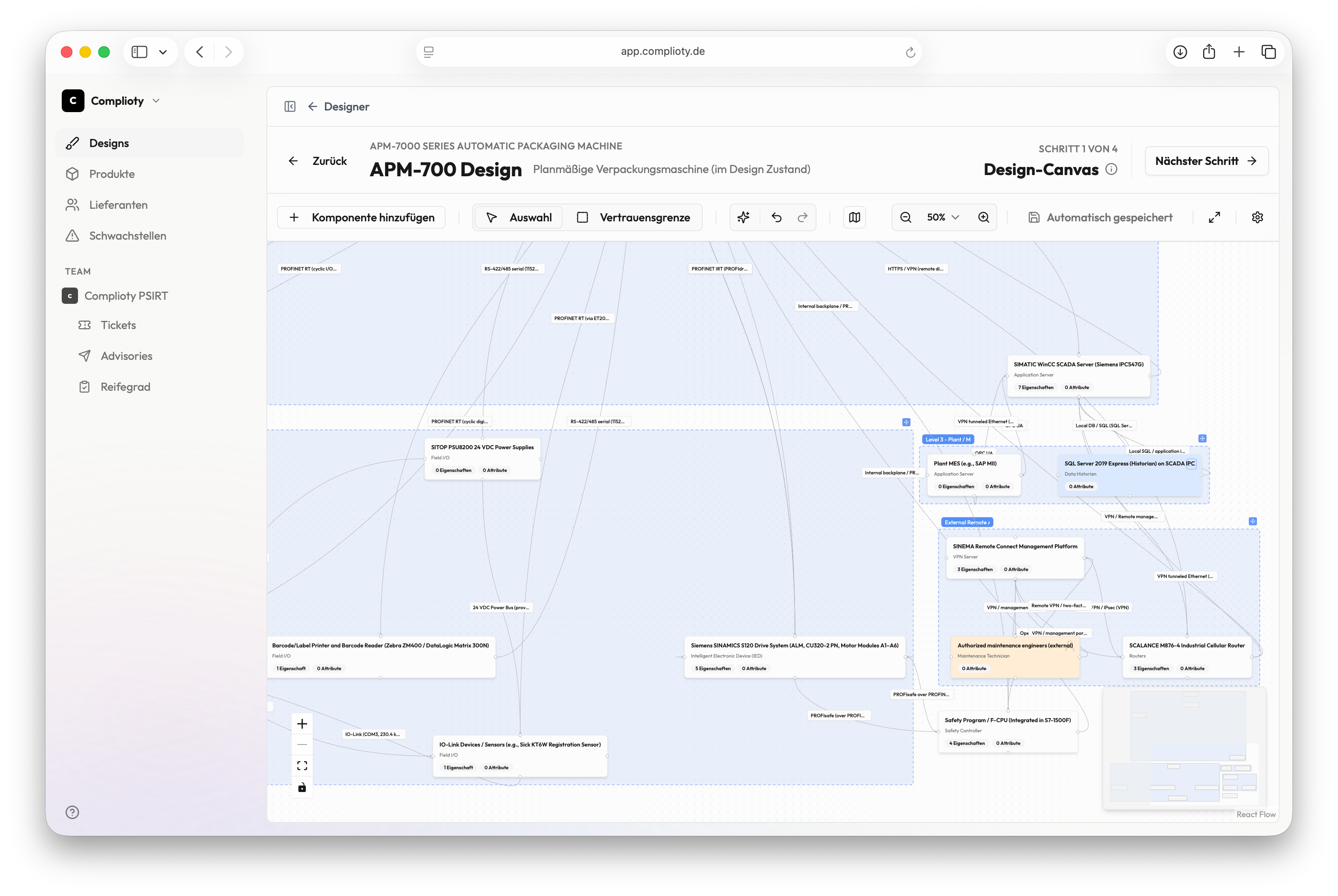
Visual Architecture Modeling
Visually model your product architecture with components, interfaces and data flows — directly in the browser.
STRIDE Analysis
Systematic threat analysis with the proven STRIDE framework. Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, Elevation of Privilege.
MITRE ATT&CK for ICS & EMB3D
Link threats to real attack techniques from MITRE ATT&CK for ICS and the EMB3D model for embedded systems.
Attacker Modeling (ISO 18045)
Define attacker profiles according to ISO 18045 — expertise, resources, motivation. Understand who you need to protect against.
Automatic Risk Assessment
Risks are automatically calculated from threat, attacker profile and damage scenario. No more manual scoring.
MITRE Mitigations & Treatment
Assign concrete countermeasures from the MITRE catalog to each threat. Traceable, standardized, audit-ready.
How Designer works
Upload product data
AI analyzes your document — PDF, DOCX, draw.io, image — and creates an initial architecture model with components and data flows.
Refine architecture
Review the AI-generated model, add trust boundaries, adjust interfaces. You refine instead of starting from scratch.
Identify threats
STRIDE and MITRE ATT&CK systematically deliver relevant threats. The AI suggests damage scenarios.
Assess risks
Attacker profiles (ISO 18045) combined with damage scenarios automatically yield the risk value — no manual scoring.
Plan & version mitigations
Assign MITRE mitigations, document treatment. Version every state — instead of rewriting.