The #1 platform for product security
Complioty connects security, compliance and product data in one continuous system — from design to operation.
Apps
Four apps. One goal.
Designer
Visually model product architectures, identify threats with STRIDE and MITRE ATT&CK, assess risks.
Learn more →Observer
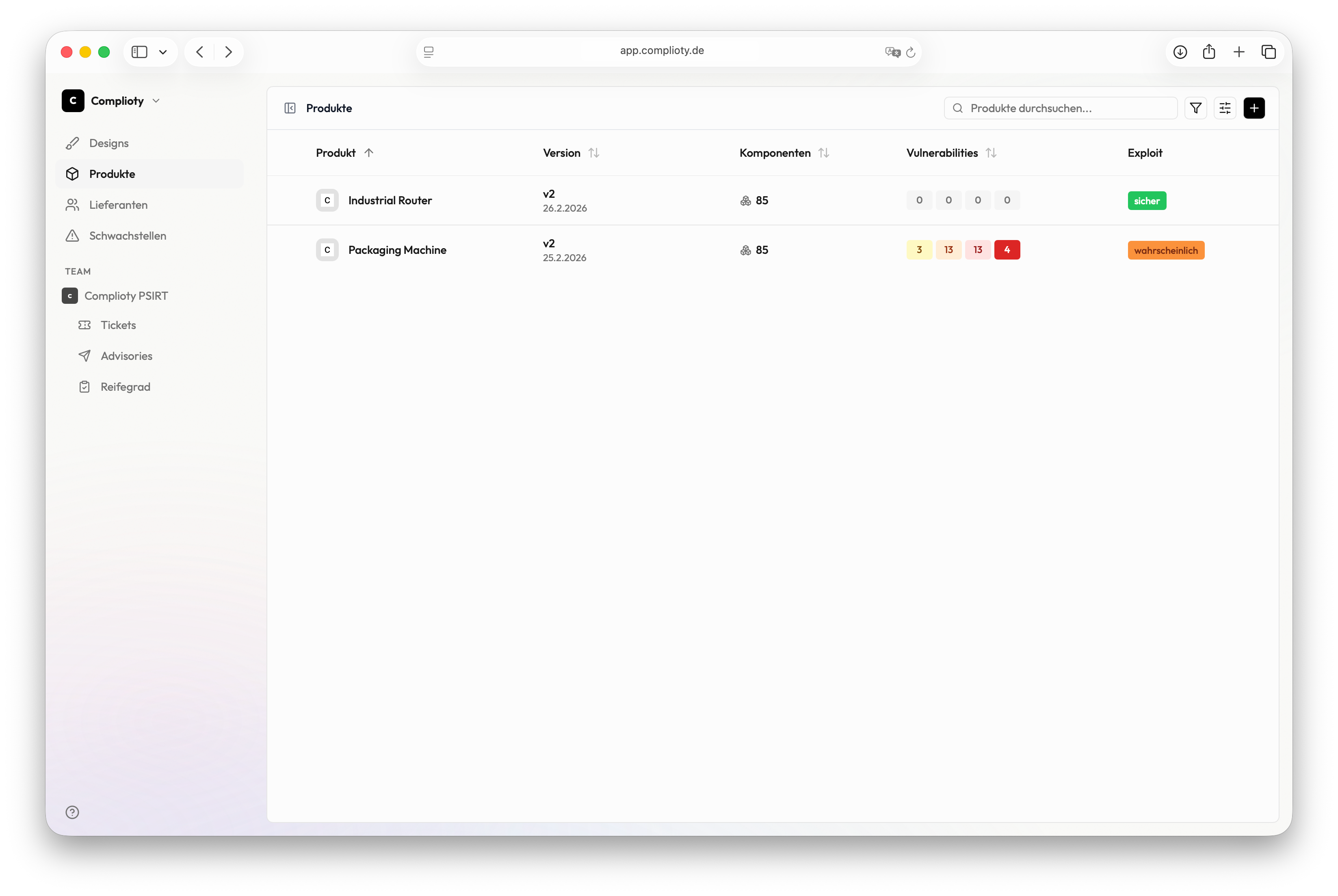
Continuous monitoring across all products and components. Automatic prioritization with CVSS and EPSS.
Learn more →Tracer
Automatic analysis of your suppliers' security maturity — an agent crawls domains and evaluates real signals.
Learn more →Notifier
Case management, CSAF advisories, security.txt and CVD policy. Structured handling from report to advisory.
Learn more →Platform
Every phase. The right apps.
Conception
Identify risks
Threat Modeling & Risk Analysis
Development
Manage vulnerabilities
CVE Monitoring & Prioritization
Supply Chain Transparency
Release
Demonstrate compliance
Compliance Documentation
Operation
Maintain security
Ongoing Vulnerability Monitoring
Supply Chain Monitoring
Coordinated Vulnerability Disclosure
Observer and Tracer accompany you from development to operation. Security is not a one-time project.
Integrations
Data in. Results out.
Complioty connects with your existing systems — as a central hub for Product Security.
SBOM / HBOM
Import components
ALM & DevOps
Repositories & Pipelines
PLM
Synchronize product data
ERP
Match master data
Notifications
Alerts & Notifications
Ticketing
Create issues & tasks
Webhooks & API
Trigger custom workflows
SBOM / HBOM
Import components
ALM & DevOps
Repositories & Pipelines
PLM
Synchronize product data
ERP
Match master data
Notifications
Alerts & Notifications
Ticketing
Create issues & tasks
Webhooks & API
Trigger custom workflows
Knowledge Sources
The world's relevant security knowledge.
Standards, laws, threat data and product knowledge. Automatically connected.
Standards & Regulation
















Threat Intelligence