How do you secure machines that operate in the field for 20 years – with components from a dozen suppliers?
Hardware, software, firmware from diverse sources. Incomplete documentation. Long lifecycles. Complioty gives you the bill of materials and the process to secure your machines across the entire product lifetime.
Complex products. Incomplete documentation. And security becomes mandatory.
You don't know what's inside
Controllers from Siemens, switches from Schneider, sensors from half a dozen suppliers. Documentation has grown over years, often incomplete. Without a full bill of materials, there is no security.
20 years of responsibility, sold once
Dozens of variants, each with its own software supply chain. Over 20 years in the field. Security updates are not a sprint — they are a marathon across the entire product lifecycle.
No process when an incident strikes
A vulnerability in a delivered machine: Who assesses? Who communicates? Who coordinates the update? Without a process, every incident becomes a fire drill — and the auditor still shows up at the door.
What an SBOM for a machine really means
Software bills of materials alone are not enough for a machine. A PLC, a switch, an industrial PC — these are hardware components with their own version states, their own vulnerabilities, their own lifecycles. We build the SBOM in three layers:
Purchased
Which components are installed? Hardware, modules, subsystems — with manufacturer, type, and version.
Self-developed
Which software did you develop yourself? PLC logic, embedded code, custom services.
Installed
Which software runs on these components? Firmware, operating systems, third-party libraries.
These three layers create the full picture. Only this way can vulnerabilities in hardware, software, and OS be continuously monitored — not just one third of them.
The right app for every phase.
No systematic threat analysis for machine architectures
Threat modeling with STRIDE and MITRE ATT&CK — directly in the architecture
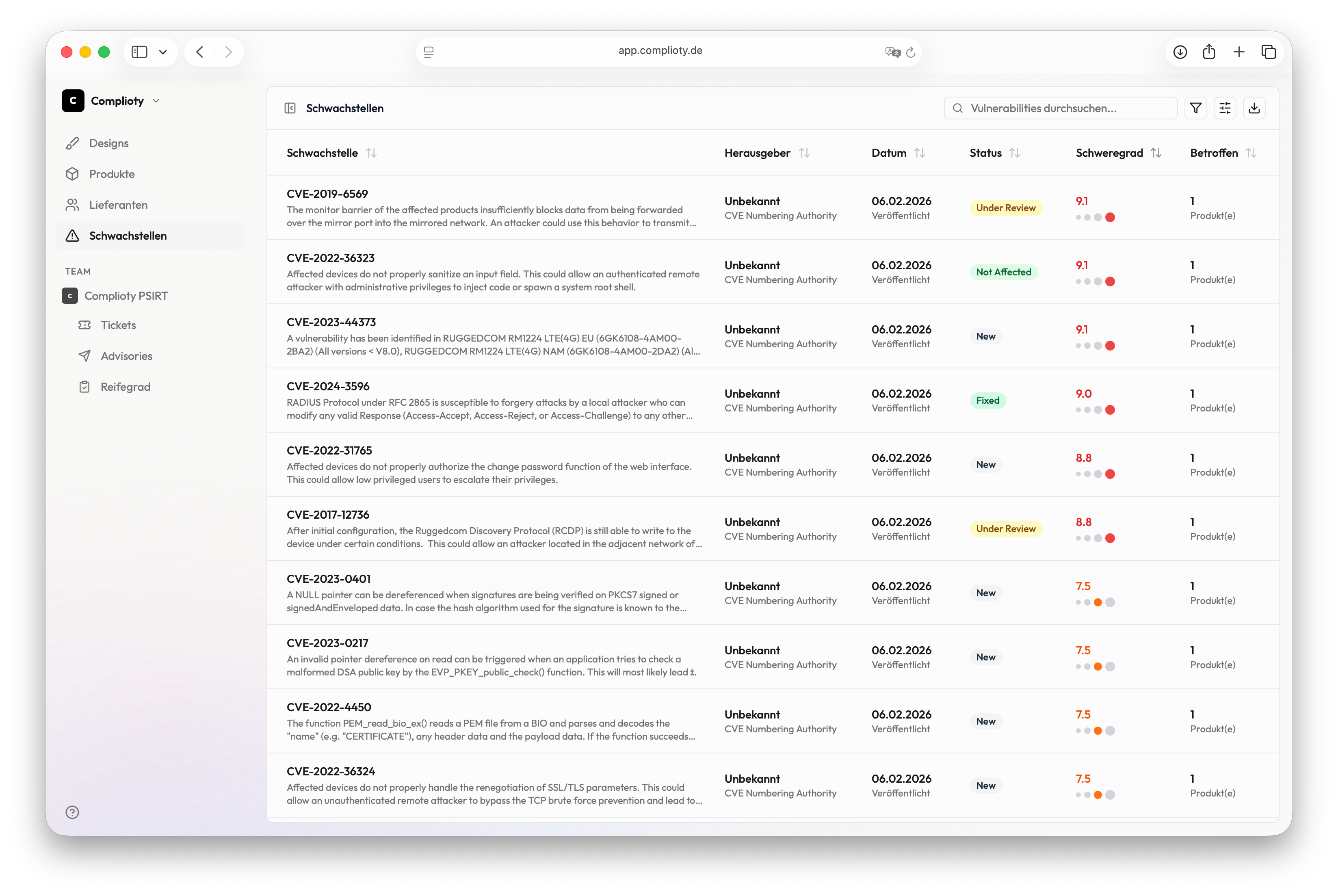
CVEs in hardware and software components are discovered too late
Automatic monitoring across all products and their complete bills of materials — including hardware, firmware, and OS
No transparency about supplier security
Supplier assessment, SBOM aggregation and risk overview in one platform
No structured process for vulnerability disclosure
Case management, CSAF advisories, security.txt and CVD policy — ready to use immediately
Scenario: CVE in a Siemens PLC
CVE discovered
Observer reports a new critical CVE in a PLC firmware used in three of your machine series.
Affected products automatically identified
Tracer immediately shows which products, batches and customer installations are affected — based on the stored SBOM.
Case opened and assessed
A case is created in Notifier. The team assesses the impact on each affected machine series and documents the decision.
Advisory created and customers notified
A CSAF advisory is generated and published on the disclosure page. Affected customers are notified automatically.
Documentation complete
The entire process is fully documented — for internal audits, CRA compliance, and customer communication.
From discovery to documented communication — in under three hours instead of three weeks.